
- www.forbes.com 77% Of Employees Report AI Has Increased Workloads And Hampered Productivity, Study Finds
Despite 96% of C-suite executives expecting AI to boost productivity, employees say it has increased their workload, hampered productivity and caused job burnout, research shows.

The new global study, in partnership with The Upwork Research Institute, interviewed 2,500 global C-suite executives, full-time employees and freelancers. Results show that the optimistic expectations about AI's impact are not aligning with the reality faced by many employees. The study identifies a disconnect between the high expectations of managers and the actual experiences of employees using AI.
Despite 96% of C-suite executives expecting AI to boost productivity, the study reveals that, 77% of employees using AI say it has added to their workload and created challenges in achieving the expected productivity gains. Not only is AI increasing the workloads of full-time employees, it’s hampering productivity and contributing to employee burnout.
- readwrite.com Reddit blocking all major search engines, except Google
%%excerpt%% Reddit has commenced its assault on search engines, blocking those that don’t have a commercial relationship with the company, like Google.

-
Automakers Sold Driver Data for Pennies, Senators Say | Ron Wyden and Edward Markey urged the F.T.C. to investigate how car companies handled the data from millions of car owners.
www.nytimes.com Automakers Sold Driver Data for Pennies, Senators SayRon Wyden and Edward Markey urged the F.T.C. to investigate how car companies handled the data from millions of car owners.

- arstechnica.com ISPs seeking government handouts try to avoid offering low-cost broadband
Despite getting subsidies, ISPs oppose $30 plans for people with low incomes.

- www.theverge.com There is no fix for Intel’s crashing 13th and 14th Gen CPUs — any damage is permanent
We got some answers from Intel, and more are on the way.

-
Switzerland mandates government agencies use open-source software and disclose the source code of software developed by or for the public sector unless third-party rights or security concerns apply
www.tomshardware.com Switzerland mandates government agencies use open-source softwareThe new law requires the use of open-source software and the publishing of new government code under open-source licenses

>Switzerland has recently enacted a law requiring its government to use open-source software (OSS) and disclose the source code of any software developed by or for the public sector. According to ZDNet, this “public body, public code” approach makes government operations more transparent while increasing security and efficiency. Such a move would likely fail in the U.S. but is becoming increasingly common throughout Europe.
>According to Switzerland’s new “Federal Law on the Use of Electronic Means for the Fulfillment of Government Tasks” (EMBAG), government agencies must use open-source software throughout the public sector.
>The new law allows the codifies allowing Switzerland to release its software under OSS licenses. Not just that; it requires the source code be released that way “unless the rights of third parties or security-related reasons would exclude or restrict this.”
>In addition to mandating the OSS code, EMBAG also requires Swiss government agencies to release non-personal and non-security-sensitive government data to the public. Calling this Open Government Data, this aspect of the new law contributes to a dual “open by default” approach that should allow for easier reuse of software and data while also making governance more transparent.
- www.yahoo.com YouTube tests server-side ads to make your coveted blocker obsolete
YouTube has been spotted testing server-side ads, which could pose a problem to ad blockers.

-
World of Warcraft developers form Blizzard’s largest, most inclusive union | 500+ employees have organized across multiple departments, creating the first wall-to-wall union of its kind at the studio
www.theverge.com World of Warcraft developers form Blizzard’s largest and most inclusive unionQA workers in Blizzard’s Austin office have also organized.

>More than 500 developers at Blizzard Entertainment who work on World of Warcraft have voted to form a union. The World of Warcraft GameMakers Guild, formed with the assistance of the Communication Workers of America (CWA), is composed of employees across every department, including designers, engineers, artists, producers, and more. Together, they have formed the largest wall-to-wall union — or a union inclusive of multiple departments and disciplines — at Microsoft.
>This news comes less than a week after the formation of the Bethesda Game Studios union, which, at the time of the announcement, was itself the largest wall-to-wall Microsoft union.
>The World of Warcraft GameMakers Guild is made up of over 500 members across Blizzard offices in California and Massachusetts. Despite its size — it is the second largest union at Microsoft overall behind Activision’s 600-member QA union — Cox said that Microsoft’s labor neutrality agreement helped get the organization ball rolling.
>Interdisciplinary unions like Blizzard’s are relatively rare, especially in the video game industry, as each department has different needs and goals. Up until this point, the majority of unionization efforts in the video game industry have been spearheaded by QA workers who have traditionally been among the least paid and least protected employees.
>The first union at Activision Blizzard was made up of QA workers, as was the first union at Microsoft’s game studios. In addition to the World of Warcraft GameMakers Guild, yet another new union made up of QA workers at Blizzard’s Austin, Texas, office has also formed. The Blizzard Quality Assurance United-CWA is a 60-person unit including QA testers for games like Diablo, Hearthstone, and other Blizzard games.
- www.lumafield.com How does a car cigarette lighter work?
Explore the engineering of a car cigarette lighter through industrial CT scans, revealing an efficient analog design that operates without digital components.
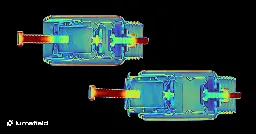
This is an ad for something CT-scan-related, but it contains a good breakdown of how an old car cigarette lighter works. And it has a couple interactive CT Scan explorers past the video.
- www.theverge.com Sonos CEO apologizes for disastrous rollout of new app
He promises frequent improvements through the fall.

I mean, he's not wrong that the app wasn't ready. Which begs the question why they didn't un-roll-it-out. >.>
- www.bbc.com How the American war on porn could change the way you use the internet
Papers please: for millions of Americans, accessing online pornography now requires a government ID. It could have global implications for the future of the web.

- www.theregister.com Data from deleted GitHub repos may not really be deleted
And the forking Microsoft-owned code warehouse doesn't see this as much of a problem

Researchers at Truffle Security have found, or arguably rediscovered, that data from deleted GitHub repositories (public or private) and from deleted copies (forks) of repositories isn't necessarily deleted.
Joe Leon, a security researcher with the outfit, said in an advisory on Wednesday that being able to access deleted repo data – such as APIs keys – represents a security risk. And he proposed a new term to describe the alleged vulnerability: Cross Fork Object Reference (CFOR).
"A CFOR vulnerability occurs when one repository fork can access sensitive data from another fork (including data from private and deleted forks)," Leon explained.
For example, the firm showed how one can fork a repository, commit data to it, delete the fork, and then access the supposedly deleted commit data via the original repository.
The researchers also created a repo, forked it, and showed how data not synced with the fork continues to be accessible through the fork after the original repo is deleted. You can watch that particular demo.
- www.computerweekly.com WhatsApp and Signal messages at risk of surveillance following EncroChat ruling, court hears | Computer Weekly
Police could lawfully use bulk surveillance techniques to access messages from encrypted communications platforms such as WhatsApp and Signal, following a ruling by the UK’s Investigatory Powers Tribunal (IPT), a court has heard.

> Police could lawfully use bulk surveillance techniques to access messages from encrypted communications platforms such as WhatsApp and Signal, following a ruling by the UK’s Investigatory Powers Tribunal (IPT), a court has heard.
- www.tomshardware.com Researchers discover battery-free technology which harvests power from radio and Wi-Fi signals for low-powered devices
Applications would result in less dependency on batteries in low-powered devices

cross-posted from: https://lemmy.ml/post/18426215
-
Wearables linked to ‘pathologic’ heart disease symptom monitoring
AFib patients using wearable devices are more likely to engage in high rates of symptom monitoring and experience anxiety than non-users, a study shows.
- www.theregister.com AI models face collapse if they overdose on their own output
Recursive training leads to nonsense, study finds

-
OopsGPT - OpenAI just announced a new search tool. Its demo already got something wrong.
www.theatlantic.com OopsGPTOpenAI just announced a new search tool. Its demo already got something wrong.
-
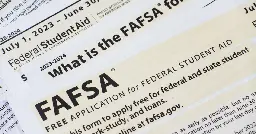
Department of Education Sued Following Markup Investigation Into FAFSA Data Shared with Facebook.
themarkup.org Department of Education Sued Following Markup Investigation Into FAFSA Data Shared with Facebook – The MarkupAdvocates want answers after The Markup found the department sharing student data with Meta
-
OpenAI: "We think there is room to make search much better than it is today. We are launching a new prototype called SearchGPT"
OpenAI: "We think there is room to make search much better than it is today. We are launching a new prototype called SearchGPT"
- 9to5google.com Reddit changes have blocked all search engines except Google amid AI 'misuse' [U]
Following a deal with Google and "misuse" of scraping its site, Reddit is now blocking all search engines from using its content.
![Reddit changes have blocked all search engines except Google amid AI 'misuse' [U]](https://lemmy.world/pictrs/image/6e935dfa-bd7e-4062-8e34-e20b8af8acd0.jpeg?format=webp&thumbnail=256)
-
AI trained on AI garbage spits out AI garbage.
www.technologyreview.com AI trained on AI garbage spits out AI garbageAs junk web pages written by AI proliferate, the models that rely on that data will suffer.
- arstechnica.com Secure Boot is completely broken on 200+ models from 5 big device makers
Keys were labeled "DO NOT TRUST." Nearly 500 device models use them anyway.

-
We finally know what caused the global tech outage - and how much it cost
www.cnn.com We finally know what caused the global tech outage - and how much it cost | CNN BusinessInsurers have begun calculating the financial damage caused by last week’s devastating CrowdStrike software glitch that crashed computers, canceled flights and disrupted hospitals all around the globe — and the picture isn’t pretty.

-
Forget security – Google's reCAPTCHA v2 is exploiting users for profit | Web puzzles don't protect against bots, but humans have spent 819 million unpaid hours solving them
www.theregister.com Google's reCAPTCHAv2 is just labor exploitation, boffins sayWeb puzzles don't protect against bots, but humans have spent 819 million unpaid hours solving them
Research Findings:
- reCAPTCHA v2 is not effective in preventing bots and fraud, despite its intended purpose
- reCAPTCHA v2 can be defeated by bots 70-100% of the time
- reCAPTCHA v3, the latest version, is also vulnerable to attacks and has been beaten 97% of the time
- reCAPTCHA interactions impose a significant cost on users, with an estimated 819 million hours of human time spent on reCAPTCHA over 13 years, which corresponds to at least $6.1 billion USD in wages
- Google has potentially profited $888 billion from cookies [created by reCAPTCHA sessions] and $8.75–32.3 billion per each sale of their total labeled data set
- Google should bear the cost of detecting bots, rather than shifting it to users
>"The conclusion can be extended that the true purpose of reCAPTCHA v2 is a free image-labeling labor and tracking cookie farm for advertising and data profit masquerading as a security service," the paper declares.
>In a statement provided to The Register after this story was filed, a Google spokesperson said: "reCAPTCHA user data is not used for any other purpose than to improve the reCAPTCHA service, which the terms of service make clear. Further, a majority of our user base have moved to reCAPTCHA v3, which improves fraud detection with invisible scoring. Even if a site were still on the previous generation of the product, reCAPTCHA v2 visual challenge images are all pre-labeled and user input plays no role in image labeling."
-
North Korean charged in ransomware attacks on US hospitals.
www.voanews.com North Korean charged in ransomware attacks on US hospitalsA grand jury in Kansas City indicted Rim Jong Hyok, accusing him of laundering ransom money and using it to fund additional cyberattacks on defense, technology and government entities around the world

- austingil.com The C̶a̶k̶e̶ User Location is a Lie!!!
A post discussing the nuances around location-based programming. Various ways to access user location, how they can fail, and what to do about it.

- arstechnica.com North Korean hacker got hired by US security vendor, immediately loaded malware
KnowBe4, which provides security awareness training, was fooled by stolen ID.

-
Anyone can Access Deleted and Private Repository Data on GitHub.
trufflesecurity.com Anyone can Access Deleted and Private Repository Data on GitHub ◆ Truffle Security Co.You can access data from deleted forks, deleted repositories and even private repositories on GitHub. And it is available forever. This is known by GitHub, and intentionally designed that way.
-
Major Labels Block 40 Pirate Domains, Search Deindexing More Concerning.
torrentfreak.com Major Labels Block 40 Pirate Domains, Search Deindexing More Concerning * TorrentFreakMajor labels are expanding site-blocking measures in France. Due to search engine deindexing, risks to internet users will only increase.
- arstechnica.com Lawsuit: T-Mobile must pay for breaking lifetime price guarantee
Class action filed over price hikes on plans with Un-contract price guarantee.

-
Microsoft has just announced a huge update to Bing that overhauls the search engine to put AI-powered answers first.
This means that when a search query is entered, the results page will pop up with a primary AI-generated answer detailing all the curated sources that have been tapped to get that result. You’ll still get the traditional search results on the Bing search page, but they will be presented to the side of the AI-generated material (in a smaller right-hand panel).
This change is currently rolling out to a small number of Bing users, but it’ll presumably become more widely available before too long. From what we can tell there’s no obvious way to turn off the AI results if you wanted to do so.
-
Google DeepMind’s AI systems can now solve complex math problems.
www.technologyreview.com Google DeepMind’s AI systems can now solve complex math problemsAlphaProof and AlphaGeometry are steps toward building systems that can reason, which could unlock exciting new capabilities.

- www.nature.com AI models collapse when trained on recursively generated data - Nature
Analysis shows that indiscriminately training generative artificial intelligence on real and generated content, usually done by scraping data from the Internet, can lead to a collapse in the ability of the models to generate diverse high-quality output.
It is now clear that generative artificial intelligence (AI) such as large language models (LLMs) is here to stay and will substantially change the ecosystem of online text and images. Here we consider what may happen to GPT-{n} once LLMs contribute much of the text found online. We find that indiscriminate use of model-generated content in training causes irreversible defects in the resulting models, in which tails of the original content distribution disappear. We refer to this effect as ‘model collapse’ and show that it can occur in LLMs as well as in variational autoencoders (VAEs) and Gaussian mixture models (GMMs). We build theoretical intuition behind the phenomenon and portray its ubiquity among all learned generative models. We demonstrate that it must be taken seriously if we are to sustain the benefits of training from large-scale data scraped from the web. Indeed, the value of data collected about genuine human interactions with systems will be increasingly valuable in the presence of LLM-generated content in data crawled from the Internet.
-
Journalists Sue Massachusetts TV Corporation Over Bogus YouTube Takedown Demands.
www.eff.org Journalists Sue Massachusetts TV Corporation Over Bogus YouTube Takedown DemandsBOSTON—A citizen journalists’ group represented by the Electronic Frontier Foundation (EFF) filed a federal lawsuit today against a Massachusetts community-access television company for falsely convincing YouTube to take down video clips of city government meetings. The lawsuit was filed in the U.S....

- www.wired.com The ACLU Fights for Your Constitutional Right to Make Deepfakes
States across the US are seeking to criminalize certain uses of AI-generated content. Civil rights groups are pushing back, arguing that some of these new laws conflict with the First Amendment.

- www.bbc.com How ordinary failure could have a seismic effect on an industrial giant
Earlier this year, a Boeing aircraft's door plug fell out in flight – all because crucial bolts were missing. The incident shows why simple failures often signal larger problems.

Earlier this year, a Boeing aircraft's door plug fell out in flight – all because crucial bolts were missing. The incident shows why simple failures like this are often a sign of larger problems, says John Downer.
