1F919 - Call Me Hand
https://www.unicode.org/charts/PDF/Unicode-9.0/U90-1F900.pdf
It's not about the money. It's about sending a message.
This is actually a thing in JoJo's Bizarre Adventure (Crazy Diamond). It's fun to see how they can make up cool scenarios with it:
Feats of this nature include trapping an enemy by restoring pieces of a broken crate around him; exposing a Stand formerly bound to an object; and tracking by restoring a severed hand, forcing it to seek out and reattach itself to the body from which it was cut off.
I remember this actually: Ted Cruz kisses his daughter... it doesn't go well
I have just dumped code into a Chrome console and saved a cert while in a pinch. It's not best practices of course, but when you need something fast for one-time use, it's nice to have something immediately available.
You could make your own webpage that works in the browser (no backend) and make a cert. I haven't published anything publicly because you really shouldn't dump private keys in unknown websites, but nothing is stopping you from making your own.
That's what NodeJS and Deno are.
The point of the browser support means it runs on modern Web technologies and doesn't need external binaries (eg: OpenSSL). It can literally run on any JS, even a browser.
Just going to mention my zero-dependency ACME (Let's Encrypt) library: https://github.com/clshortfuse/acmejs
It runs on Chrome, Safari, FireFox, Deno, and NodeJS.
I use it to spin up my wildcard and HTTP certificates. I've personally automated it by having the certificate upload to S3 buckets and AWS Certificates. I wrote a helper for Name.com for DNS validation. For HTTP validation, I use HTTP PUT.
Pippi Longstocking
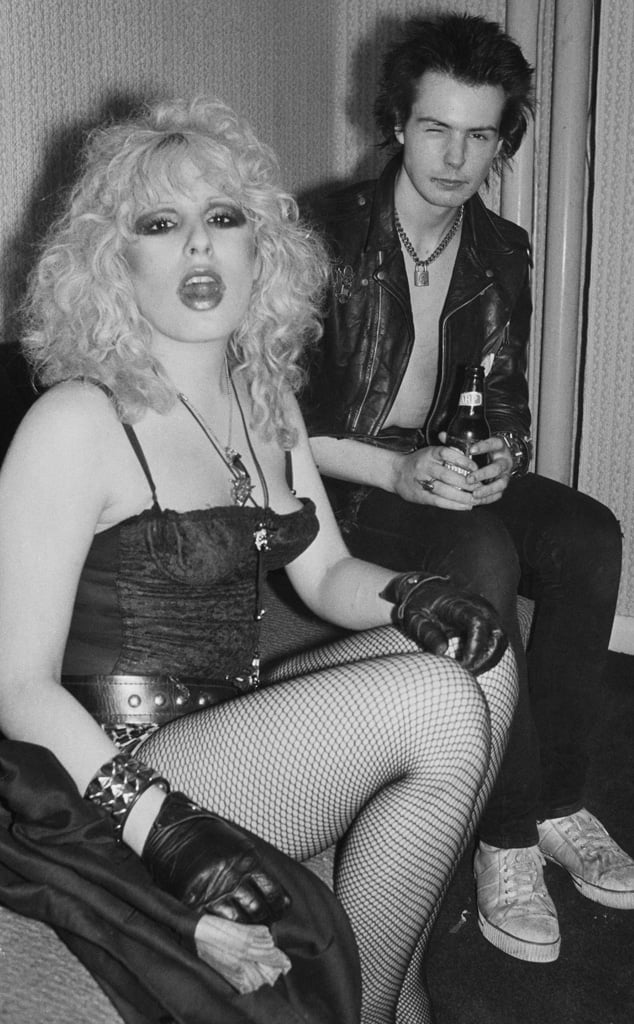
I mean, you can find 70s punk images just like this. I'm sure some are already great-grand parents. Nancy and Sid are from 1977:
Also, Hitler was humorless? I heard when he came to town, people had a gas.
/sorry
I can spend 2 minutes scanning a page for a certain word every time I need to search for something.
But I'm very happy somebody spent the time to code Ctrl+F.
Windows 10 and it's not a good idea
Don't use JSON for the response unless you include the response header to specify it's application/json. You're better off with regular plaintext unless the request header Accept asked for JSON and you respond with the right header.
That also means you can send a response based on what the request asked for.
403 Forbidden (not Unauthorized) is usually enough most of the time. Most of those errors are not meant for consumption by an application because it's rare for 4xx codes to have a contract. They tend to go to a log and output for human readers later, so I'd lean on text as default.
While
Whyle
Whyull
Yull
Yul