-
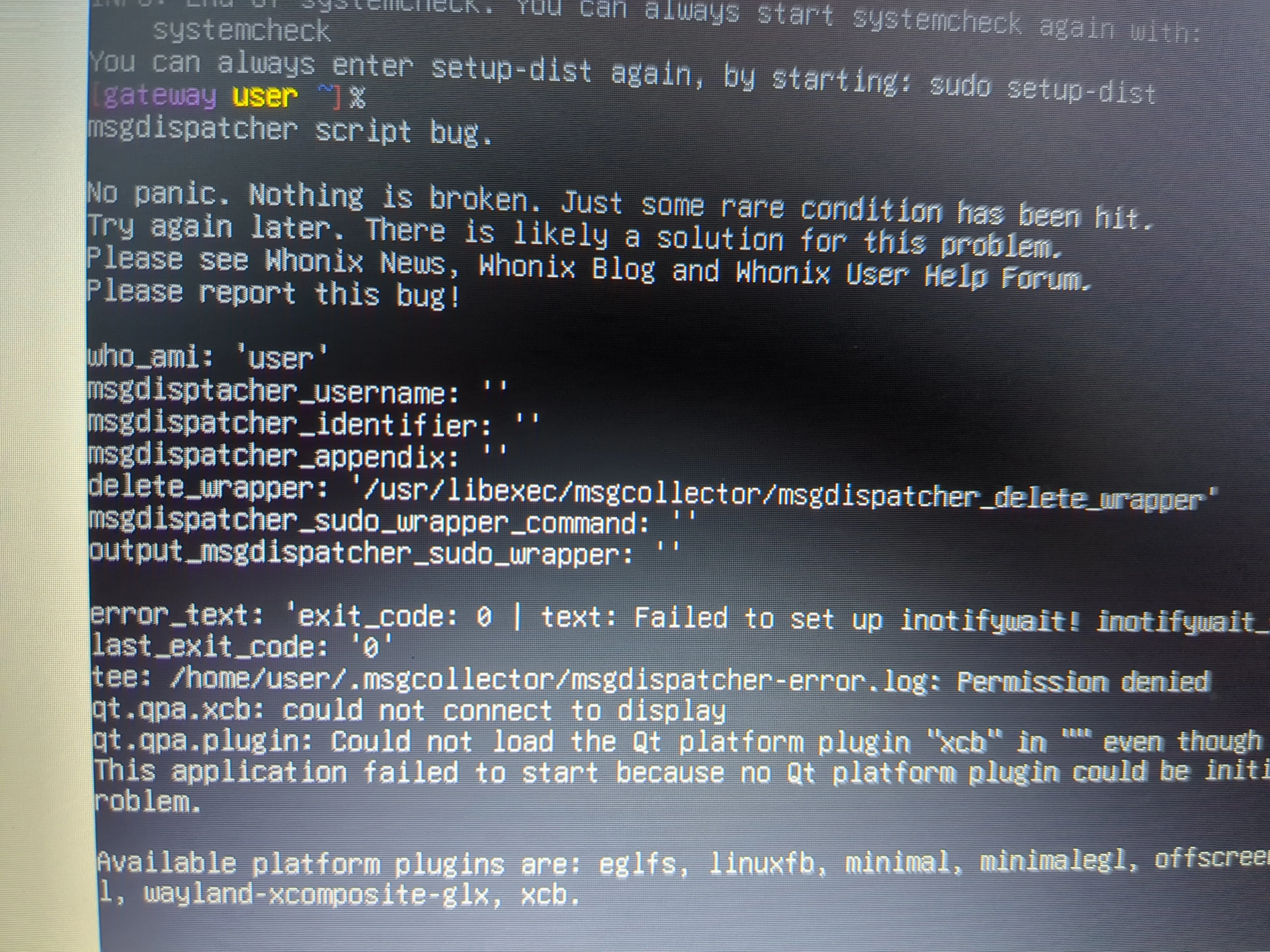
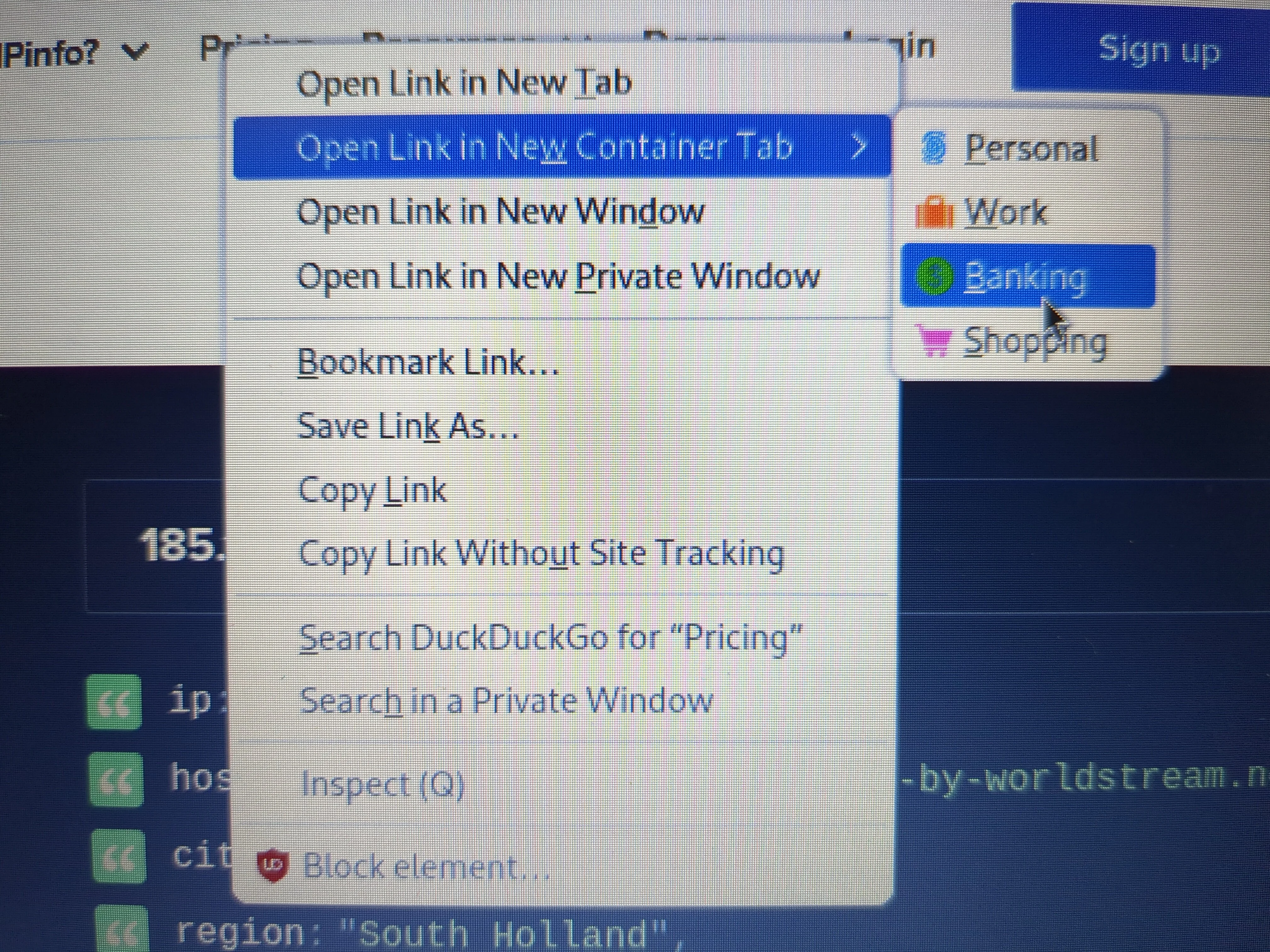
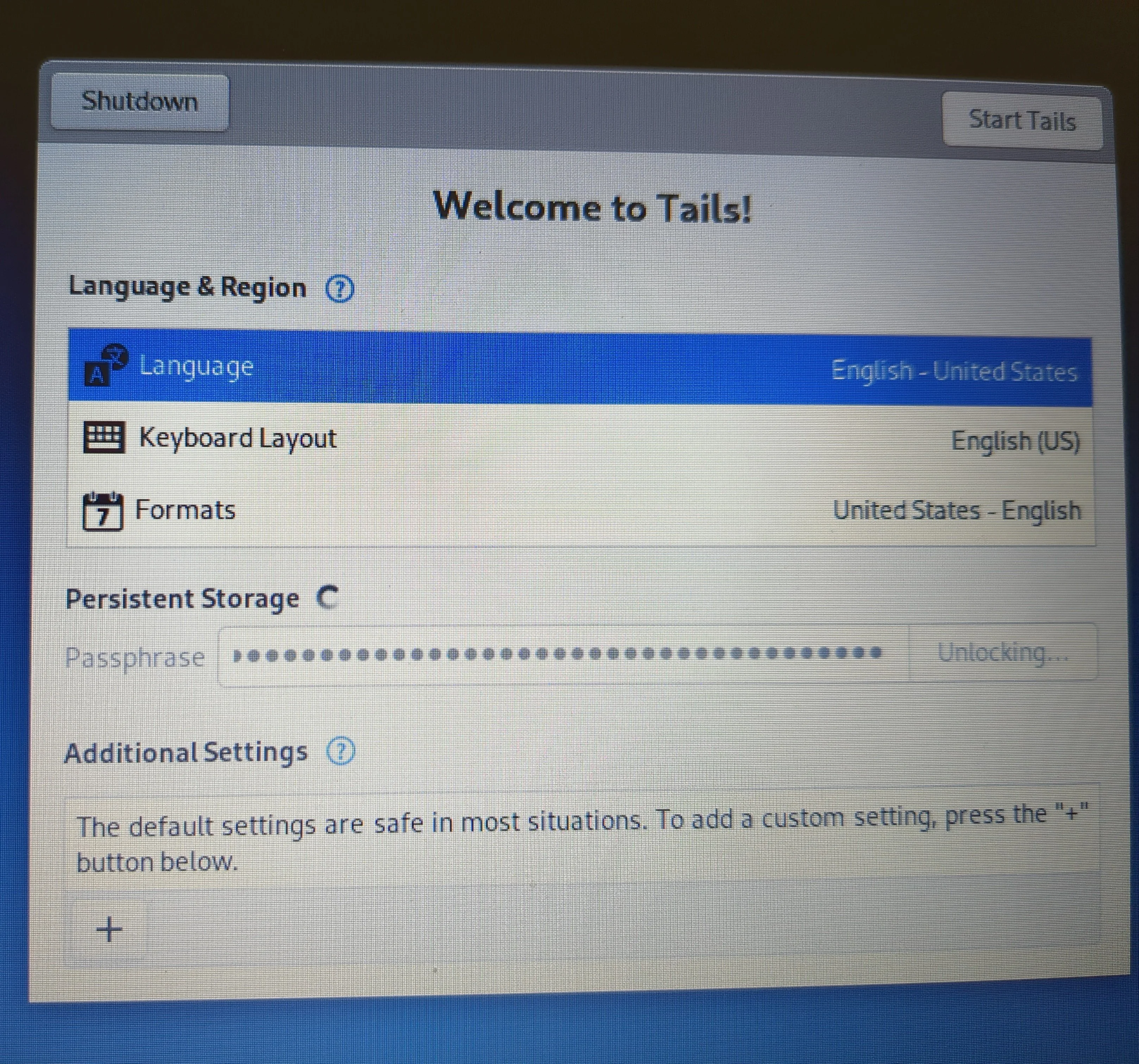
TAILS development
Arti (Rust memory hardened code) https://lemmy.world/post/17930434 Keystroke Deanonymization https://lemmy.world/post/17672429
-
Augmented Reality and VR
A few decades and exciting new worlds to explore, sensorially indistinguishable from IRL? https://lemmy.world/pictrs/image/e5e3626b-d8bf-4d71-9867-90d3b23e33ee.jpeg
-
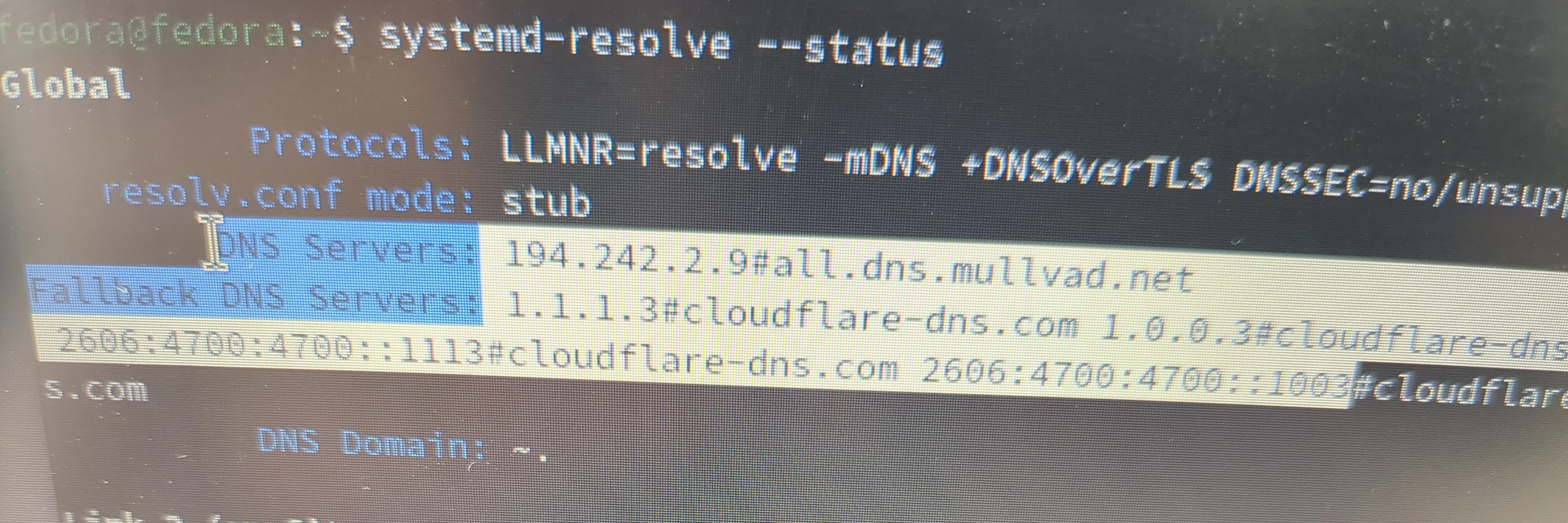
Attestation and Fedora hardening
discussion.fedoraproject.org Confidential Computing, Attestation, and HSI TestsIf there is anyone who is interested in the research of the invisiblethingslab.com, confidential computing, and firmware security, please reply with information about how to implement attestation and kernel and firmware lockdowns in Fedora. I am interested in protecting a system from cold boot atta...

-
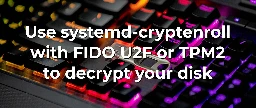
Qubes LUKS and FIDO
forum.qubes-os.org Lock LUKS with Nitrokey FIDO U2F - which dracut method?Does anyone foresee any obstacles in implementing a U2F security key lock on Qubes OS LUKS? Systemd has cryptenroll. This is probably as close to trusted boot / U2F secured power up as a Qubes computer could get without HEADS BIOS. This way, at least as long as you keep your security key, no o...
-
Qubes Certification for EMI hardened hardware
www.qubes-os.org Certified hardwareThe Qubes OS Project aims to partner with a select few computer vendors to ensure that Qubes users have reliable hardware purchasing options. We aim for these vendors to be as diverse as possible in terms of geography, cost, and availability. Warning: The Qubes OS Project certifies only...

Certain computing platforms like smart phones are more resilient when it comes to EMI/EMC (harmful electromagnetic interference) than others. Defense computers, for example, are designed to meet specifications like TEMPEST and MIL-STD-461. Although "Qubes Air" or cloud Qubes which could run on a cellular platform has been proposed, more development is required. Defense computers like Roda or GRiD can be found on eBay and from government surplus but the models do not have sufficient CPU power (core2duo in the instances I have seen which is close to Pentium and not nearly the i5 / i7 Intels required). There are also EMI shielding sprays with silver particles that might be applied to consumer laptops as another alternative to explore. Other than that, does anyone have ideas about creating an EMI fortified platform prototype that would be compatible with Qubes?
https://www.roda-computer.com/technology/mil-std-standards/
https://www.griduk.com/
https://forum.qubes-os.org/t/qubes-air-qubes-in-the-cloud/921
https://mgchemicals.com/products/conductive-paint/conductive-spray-paint/emi-shielding/
-
Why do you think the Polish got good at BIOS?
3mdeb.com 3mdeb | Our open source software your solution"Your Trusted Partner in Embedded Systems and Firmware Security. Enhance your product's with our consulting services, firmware development, and hardware design."
note the Polish names https://invisiblethingslab.com/ "Low level" i.e. BIOS, EC, firmware
Qubes Certified with latest 12th gen Intel i5/i7 CPUs https://novacustom.com/product/nv41-series/ (laptop) https://shop.3mdeb.com/shop/open-source-hardware/dasharo-fidelisguard-z690-qubes-os-certified/ (desktop) [RAM greater than or equal to 16GB required. VM sys qubes can be configured for lighter memory use. 32 GB of RAM is what these systems ship with and you wouldn't need to tailor qube utilization. But, really, the i5/i7 CPU is the most important part for Qubes compatibility.]
Polish Firmware Companies https://3mdeb.com/ https://www.dasharo.com/
-
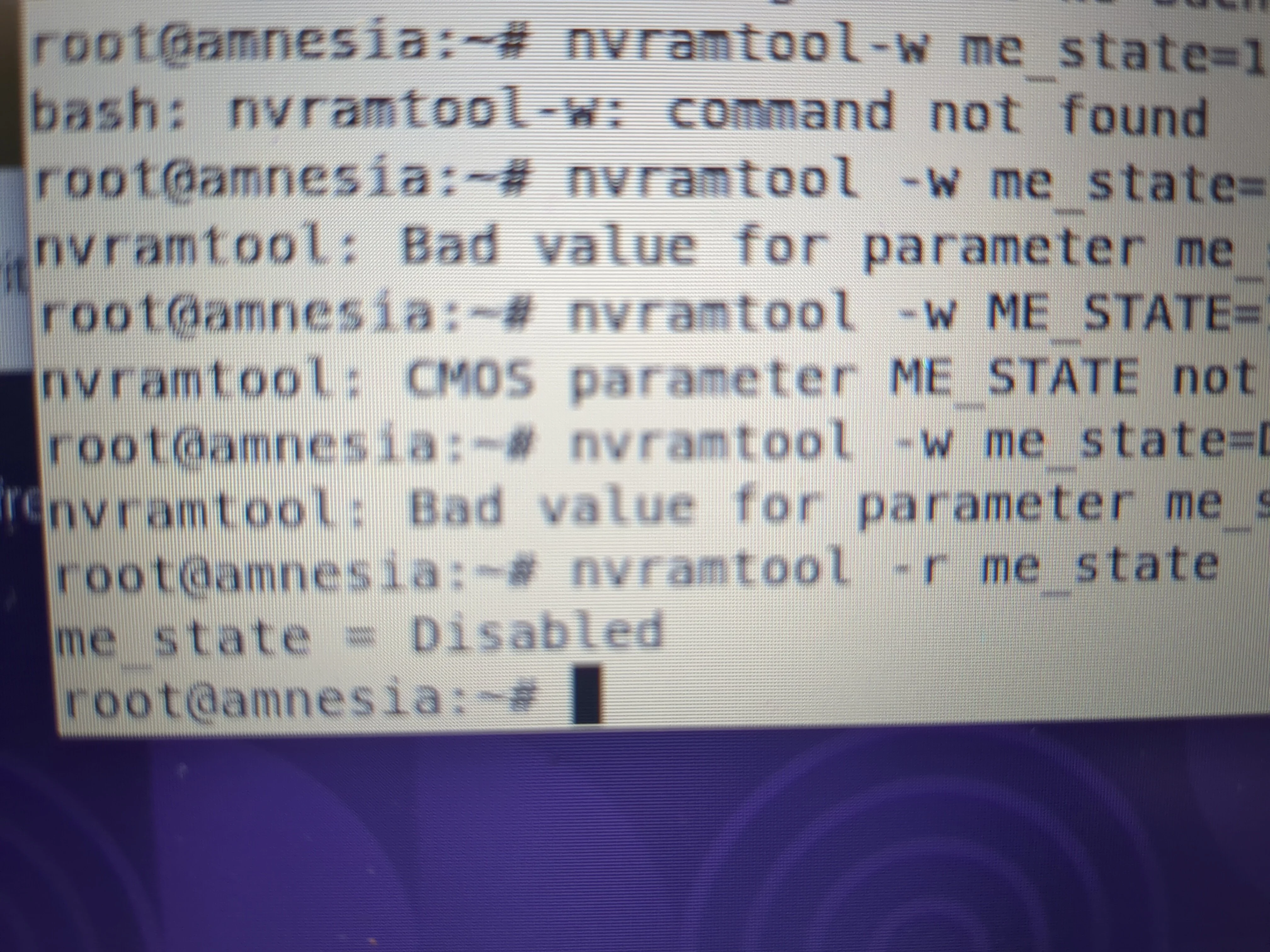
Firmware Cyber Trust and Libreboot
www.osfc.io US Cyber Trust Mark: Is your firmware ready? - OSFCChange the way of firmware development, collaborate with others and share knowledge.
Hardened Grub in Libreboot https://libreboot.org/docs/linux/grub_hardening.html
See Mate Kukri at upcoming Open Source Firmware Conference about TPM compromise.
https://libreboot.org/docs/install/spi.html Ready to get out your pi and external programmer? https://en.m.wikipedia.org/wiki/CryptoParty